CloudFlare servers in India get MITMd by the network provider (probably Airtel) if the upstream is GitHub Pages and configured without end-to-end TLS.
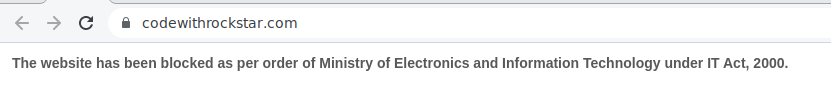
So I get the following with a padlock:
Here's a detailed curl log:
Curl Log
curl -vvv https://codewithrockstar.com/
* Trying 172.67.209.159...
* TCP_NODELAY set
* Connected to codewithrockstar.com (172.67.209.159) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /etc/ssl/certs/ca-certificates.crt
CApath: /etc/ssl/certs
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Unknown (8):
* TLSv1.3 (IN), TLS handshake, Certificate (11):
* TLSv1.3 (IN), TLS handshake, CERT verify (15):
* TLSv1.3 (IN), TLS handshake, Finished (20):
* TLSv1.3 (OUT), TLS change cipher, Client hello (1):
* TLSv1.3 (OUT), TLS Unknown, Certificate Status (22):
* TLSv1.3 (OUT), TLS handshake, Finished (20):
* SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384
* ALPN, server accepted to use h2
* Server certificate:
* subject: C=US; ST=California; L=San Francisco; O=Cloudflare, Inc.; CN=sni.cloudflaressl.com
* start date: Jun 11 00:00:00 2021 GMT
* expire date: Jun 10 23:59:59 2022 GMT
* subjectAltName: host "codewithrockstar.com" matched cert's "codewithrockstar.com"
* issuer: C=US; O=Cloudflare, Inc.; CN=Cloudflare Inc ECC CA-3
* SSL certificate verify ok.
* Using HTTP2, server supports multi-use
* Connection state changed (HTTP/2 confirmed)
* Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
* Using Stream ID: 1 (easy handle 0x55636c7b3580)
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
> GET / HTTP/2
> Host: codewithrockstar.com
> User-Agent: curl/7.58.0
> Accept: */*
>
* TLSv1.3 (IN), TLS Unknown, Certificate Status (22):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS handshake, Newsession Ticket (4):
* TLSv1.3 (IN), TLS Unknown, Unknown (23):
* Connection state changed (MAX_CONCURRENT_STREAMS updated)!
* TLSv1.3 (OUT), TLS Unknown, Unknown (23):
* TLSv1.3 (IN), TLS Unknown, Unknown (23):
< HTTP/2 200
< date: Wed, 08 Dec 2021 05:15:48 GMT
< content-type: text/html
< pragma: no-cache
< cache-control: no-cache
< cf-cache-status: DYNAMIC
< expect-ct: max-age=604800, report-uri="https://report-uri.cloudflare.com/cdn-cgi/beacon/expect-ct"
< report-to: {"endpoints":[{"url":"https:\/\/a.nel.cloudflare.com\/report\/v3?s=bcSTAfe2Bi%2F8SS9j%2FEp6ZUbz28rFoVCW7jE2PLYQYlBzsDr14vnr3Y6Gazh8pwXAUx8WFaW6e7duAr47%2FEk6ETrFutpg2lNa%2BBQ1zqMjvuHzU2pTq%2Fz6QYZIvofco5SeI7t84M0%2BQw%3D%3D"}],"group":"cf-nel","max_age":604800}
< nel: {"success_fraction":0,"report_to":"cf-nel","max_age":604800}
< server: cloudflare
< cf-ray: 6ba3849b4fdb4ae7-HYD
< alt-svc: h3=":443"; ma=86400, h3-29=":443"; ma=86400, h3-28=":443"; ma=86400, h3-27=":443"; ma=86400
<
* TLSv1.3 (IN), TLS Unknown, Unknown (23):
* Connection #0 to host codewithrockstar.com left intact
<style>body{margin:0px;padding:0px;}iframe{width:100%;height:100%}</style><iframe src="https://www.airtel.in/dot/" width="100%" height="100%" frameborder=0></iframe>
CloudFlare has known about this issue for years (actively hostile ISPs) and they don't seem to be doing anything about it. The two fixes here are:
- Switch from CloudFlare to direct GitHub Pages, which supports TLS now.
- Enable HTTPS on GitHub pages, and switch the upstream on CloudFlare to get strict SSL instead of flexible.
Here's a very similar block story:
CloudFlare servers in India get MITMd by the network provider (probably Airtel) if the upstream is GitHub Pages and configured without end-to-end TLS.
So I get the following with a padlock:
Here's a detailed curl log:
Curl Log
curl -vvv https://codewithrockstar.com/ * Trying 172.67.209.159... * TCP_NODELAY set * Connected to codewithrockstar.com (172.67.209.159) port 443 (#0) * ALPN, offering h2 * ALPN, offering http/1.1 * successfully set certificate verify locations: * CAfile: /etc/ssl/certs/ca-certificates.crt CApath: /etc/ssl/certs * TLSv1.3 (OUT), TLS handshake, Client hello (1): * TLSv1.3 (IN), TLS handshake, Server hello (2): * TLSv1.3 (IN), TLS Unknown, Certificate Status (22): * TLSv1.3 (IN), TLS handshake, Unknown (8): * TLSv1.3 (IN), TLS handshake, Certificate (11): * TLSv1.3 (IN), TLS handshake, CERT verify (15): * TLSv1.3 (IN), TLS handshake, Finished (20): * TLSv1.3 (OUT), TLS change cipher, Client hello (1): * TLSv1.3 (OUT), TLS Unknown, Certificate Status (22): * TLSv1.3 (OUT), TLS handshake, Finished (20): * SSL connection using TLSv1.3 / TLS_AES_256_GCM_SHA384 * ALPN, server accepted to use h2 * Server certificate: * subject: C=US; ST=California; L=San Francisco; O=Cloudflare, Inc.; CN=sni.cloudflaressl.com * start date: Jun 11 00:00:00 2021 GMT * expire date: Jun 10 23:59:59 2022 GMT * subjectAltName: host "codewithrockstar.com" matched cert's "codewithrockstar.com" * issuer: C=US; O=Cloudflare, Inc.; CN=Cloudflare Inc ECC CA-3 * SSL certificate verify ok. * Using HTTP2, server supports multi-use * Connection state changed (HTTP/2 confirmed) * Copying HTTP/2 data in stream buffer to connection buffer after upgrade: len=0 * TLSv1.3 (OUT), TLS Unknown, Unknown (23): * TLSv1.3 (OUT), TLS Unknown, Unknown (23): * TLSv1.3 (OUT), TLS Unknown, Unknown (23): * Using Stream ID: 1 (easy handle 0x55636c7b3580) * TLSv1.3 (OUT), TLS Unknown, Unknown (23): > GET / HTTP/2 > Host: codewithrockstar.com > User-Agent: curl/7.58.0 > Accept: */* > * TLSv1.3 (IN), TLS Unknown, Certificate Status (22): * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * TLSv1.3 (IN), TLS handshake, Newsession Ticket (4): * TLSv1.3 (IN), TLS Unknown, Unknown (23): * Connection state changed (MAX_CONCURRENT_STREAMS updated)! * TLSv1.3 (OUT), TLS Unknown, Unknown (23): * TLSv1.3 (IN), TLS Unknown, Unknown (23): < HTTP/2 200 < date: Wed, 08 Dec 2021 05:15:48 GMT < content-type: text/html < pragma: no-cache < cache-control: no-cache < cf-cache-status: DYNAMIC < expect-ct: max-age=604800, report-uri="https://report-uri.cloudflare.com/cdn-cgi/beacon/expect-ct" < report-to: {"endpoints":[{"url":"https:\/\/a.nel.cloudflare.com\/report\/v3?s=bcSTAfe2Bi%2F8SS9j%2FEp6ZUbz28rFoVCW7jE2PLYQYlBzsDr14vnr3Y6Gazh8pwXAUx8WFaW6e7duAr47%2FEk6ETrFutpg2lNa%2BBQ1zqMjvuHzU2pTq%2Fz6QYZIvofco5SeI7t84M0%2BQw%3D%3D"}],"group":"cf-nel","max_age":604800} < nel: {"success_fraction":0,"report_to":"cf-nel","max_age":604800} < server: cloudflare < cf-ray: 6ba3849b4fdb4ae7-HYD < alt-svc: h3=":443"; ma=86400, h3-29=":443"; ma=86400, h3-28=":443"; ma=86400, h3-27=":443"; ma=86400 < * TLSv1.3 (IN), TLS Unknown, Unknown (23): * Connection #0 to host codewithrockstar.com left intact <style>body{margin:0px;padding:0px;}iframe{width:100%;height:100%}</style><iframe src="https://www.airtel.in/dot/" width="100%" height="100%" frameborder=0></iframe>CloudFlare has known about this issue for years (actively hostile ISPs) and they don't seem to be doing anything about it. The two fixes here are:
Here's a very similar block story: