Wkd now uses advanced request where possible and checks policy file#3033
Wkd now uses advanced request where possible and checks policy file#3033
Conversation
 tomholub
left a comment
tomholub
left a comment
There was a problem hiding this comment.
Looks great, a small change regarding reporting
|
It's really likely misconfiguration on his end. Policy has no CORS: But the end file has proper cors: Therefore we should still be polling the policy file if we want to follow the spec. To be fair, if a lot of WKD servers are misconfigured also, we may drop reading the policy file. For now, let's try to follow. |
|
I will switch it to test another email |
|
Thanks! I'll have a look at the remaining error report, it may be hard for you to hunt down. |
| } | ||
| return { pubkey: null, pgpClient: null }; | ||
| } | ||
| } |
There was a problem hiding this comment.
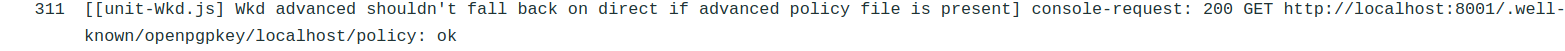
@rrrooommmaaa I think the error was here: if I'm reading it correctly, it was possible for the for loop to finish and validUrl would remain undefined. Then the lines below would continue calling that URL like undefined/hu/... causing the error reports.
I recommend to try to avoid for loops that do accounting in this manner unless one really cannot avoid them. It can be hard to spot bugs. I've rewritten it as a method that gets called two times explicitly with two different parameters (advanced vs direct url), which I think will make for an easier to debug structure.
|
I'll do some more improvements to the browser tests in general while I'm at it (our tests are a bit complex, sorry about that) |
Closes #3003
First checks for policy file, then extracts the key and checks for email match.
Advanced method is now supported.